Table of contents
MPLS, or Multiprotocol Label Switching, is a networking method that moves traffic through a network by attaching short labels to packets. Instead of making every router inspect the full destination IP address, MPLS lets routers forward packets by reading the label and sending the traffic along a predefined path.
In simple terms, MPLS is a way to make WAN traffic more predictable. It is commonly used when businesses need private site-to-site connectivity, stable latency, QoS support, and service-level guarantees from a network provider.
In standard IP routing, every router performs a longest-prefix match (LPM) on the destination address. That lookup time varies with routing table size. MPLS eliminates per-hop IP lookups. Instead, a short label decides the next hop.
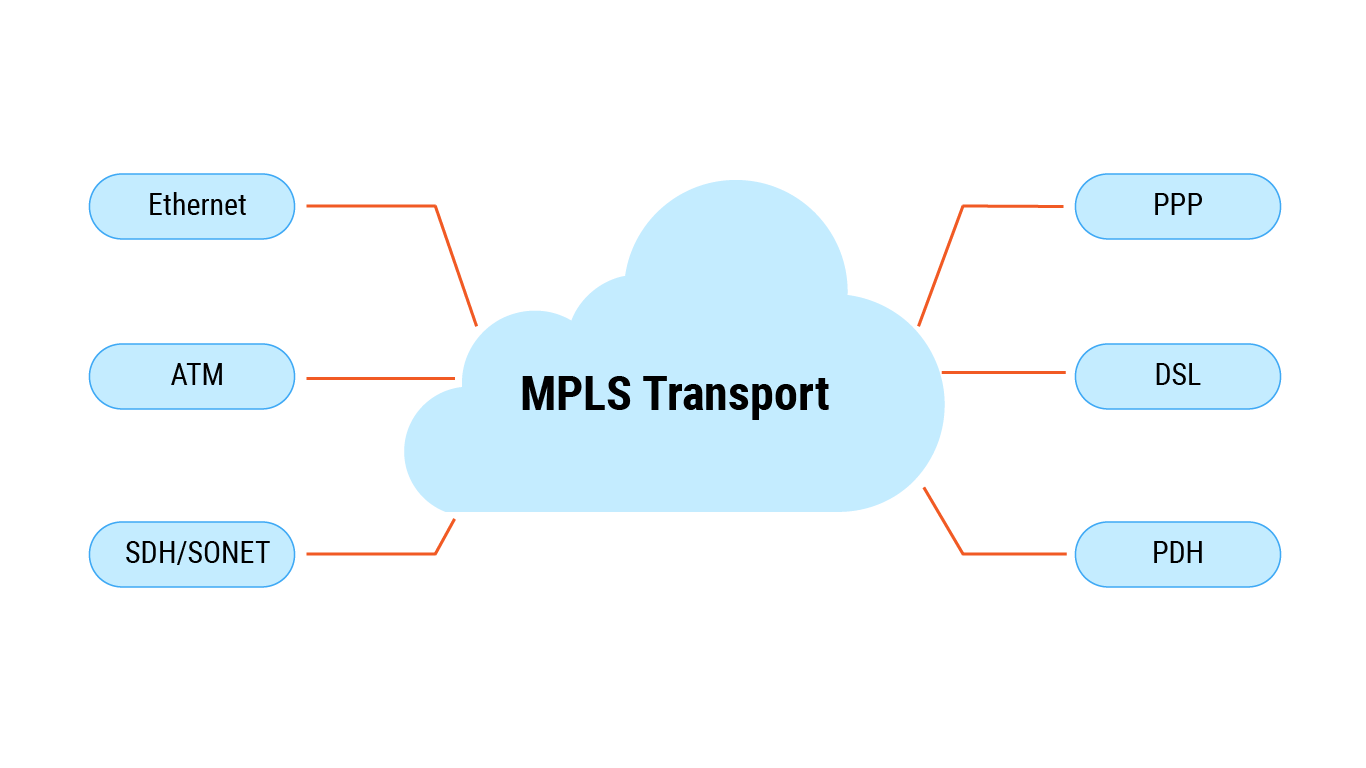
The label sits between the Layer 2 and Layer 3 headers. Hence the description Layer 2.5 protocol. “Multiprotocol” means the same backbone can carry IPv4, IPv6, Ethernet, ATM, or Frame Relay.
This is the core MPLS meaning in networking: packets from different services can cross the same provider backbone while being forwarded according to labels rather than repeated IP routing decisions.
From a buyer’s perspective, an MPLS circuit is a private connection over a provider’s MPLS cloud. The provider manages labels internally; the customer sees only reliable edge-to-edge transport.
An MPLS network is the provider-managed or enterprise-managed backbone where label switching takes place. The customer normally does not manage the internal labels or label-switched paths; they consume the result as a private WAN service.
An MPLS service is the commercial connectivity product delivered over that backbone. Depending on the provider, it may be sold as MPLS VPN, MPLS L3VPN, private WAN connectivity, SLA-backed transport, or an MPLS circuit between business locations.
A less-known fact: the initial MPLS standard (RFC 3031) deliberately avoided tying labels to a specific routing protocol, which is why today it works equally well with OSPF, IS-IS, and BGP.
Why MPLS was created
In the mid-1990s, core routers relied on software-based IP lookups. As internet traffic grew, those lookups became a bottleneck. ATM switching offered speed but was complex and protocol-specific. MPLS emerged as a compromise: the speed of label switching, like ATM, with the flexibility of IP. It allowed service providers to forward traffic at wire speed while still supporting multiple network protocols.
Two decades later, that original value proposition — speed + flexibility — remains valid, though today’s hardware makes label lookup less about raw speed and more about deterministic forwarding.
At a high level, MPLS does three things: it classifies traffic at the network edge, attaches a label that represents how the packet should be handled, and forwards that packet through the backbone by swapping labels at each MPLS router. This is why MPLS is often described as label-based forwarding rather than destination-based routing.
Every MPLS packet undergoes three sequential handling actions: label imposition, often called push, label swapping, swap, and label removal, pop. Their locations differ.
| Action | Performed at | Result |
|---|---|---|
| Imposition | Ingress LER | One or more labels attached |
| Swapping | Core LSR | Incoming label replaced with outgoing counterpart |
| Removal | Egress LER | Top label or stack taken off |
Forwarding steps
Once traffic enters an MPLS domain, the packet is handled differently at the edge and in the core. The edge routers make the service decision, while the core routers mainly follow label instructions.
Ingress LER / PE router – this is the first MPLS-aware device that receives the customer packet. It checks the relevant packet information, such as the destination prefix, policy rules, or QoS markings, and places the packet into a Forwarding Equivalence Class (FEC). Based on that classification, the router adds one or more MPLS labels. In provider networks, this device is commonly called an ingress PE router because it sits at the boundary between the customer network and the provider MPLS backbone.
Core LSR / P routers – after the label has been added, the packet moves through the MPLS core. Transit routers do not need to make a full customer IP routing decision for every packet. Instead, each router uses the incoming label as a local forwarding instruction: it maps that label to an outgoing interface and, when needed, replaces it with the next label in the path. These core routers are often called P routers because they operate inside the provider network rather than at the customer edge.
Egress LER / PE router – at the far side of the MPLS domain, the final edge router recognises that the labelled transport across the provider backbone is complete. It removes the MPLS label, or the relevant part of the label stack, and hands the original traffic toward the destination customer site or downstream network. In provider terminology, this device is the egress PE router.
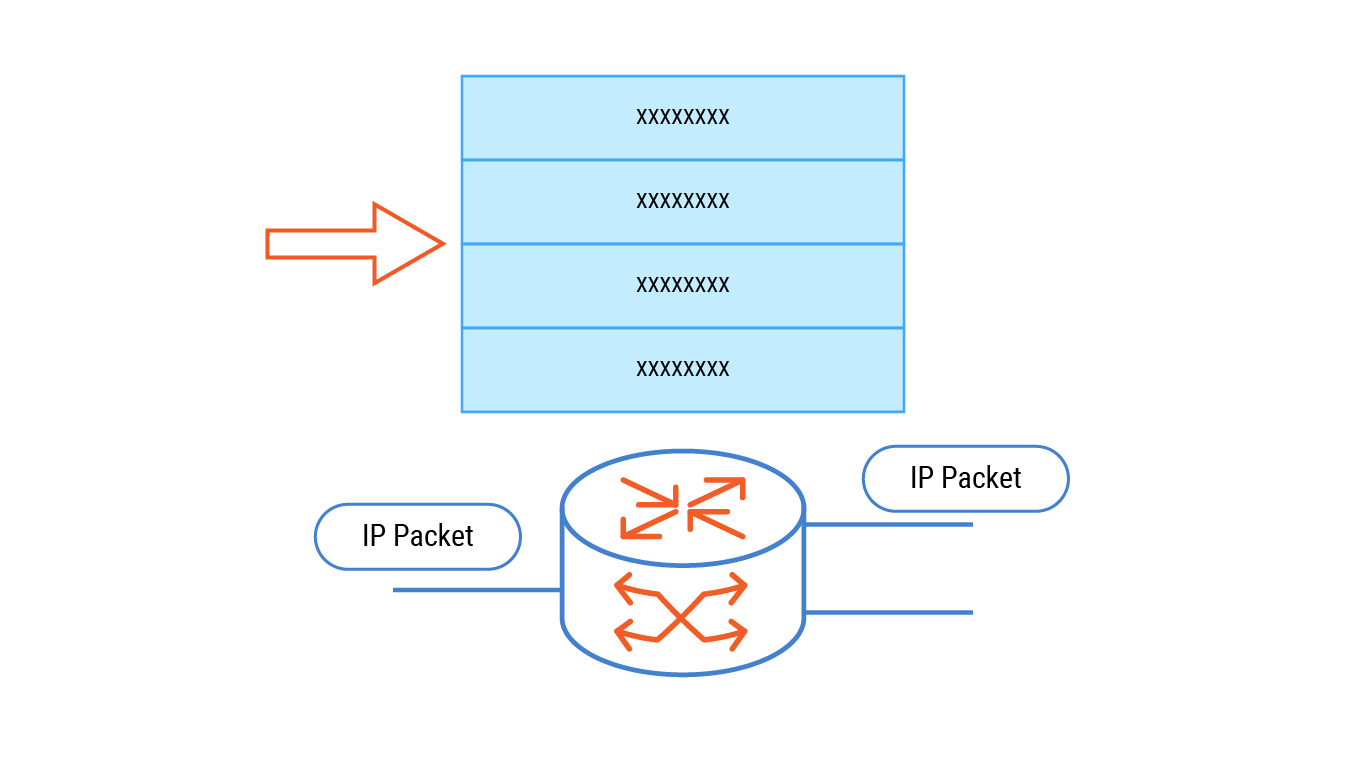
IP routing uses software for IP lookups to find the next hop, resulting in low forwarding performance.
The route followed inside the MPLS backbone is called a Label Switched Path (LSP). An LSP is built in one direction, so return traffic normally uses a separate path unless a bidirectional LSP is configured. These paths can be created dynamically with LDP, which follows the underlying IGP topology, or engineered more deliberately with RSVP-TE when the operator needs explicit route control. Because packets in the same FEC use the same LSP, MPLS can provide more consistent delay and packet ordering than ordinary best-effort forwarding.
Key MPLS Components: Labels, FEC, and LSPs
MPLS works because several control and forwarding elements operate together. Labels tell routers where to send packets, FECs define which packets should receive the same treatment, and LSPs provide the actual path through the MPLS network. Understanding these components makes the packet flow easier to follow.
32-bit label stack entry
Every MPLS packet carries at least one label stack entry. This entry is small — only 32 bits — but it contains the information needed for forwarding, service handling, QoS treatment, and loop prevention.
| Field | Bits | Role |
|---|---|---|
| Label | 20 | Forwarding value |
| Traffic Class | 3 | QoS priority, formerly EXP |
| Bottom of Stack (BoS) | 1 | Last label flag |
| TTL | 8 | Hop limit |
The label stack entry is read by MPLS routers as the packet moves through the network. In most cases, core routers only need the top label to make a forwarding decision, which keeps forwarding behaviour simple and predictable.
Label – locally significant integer. Bindings exchanged via LDP or RSVP-TE. Labels can be stacked: outer for tunnelling, inner for VPN/service.
FEC (Forwarding Equivalence Class) – group of packets treated identically. Ingress LER decides FEC based on destination prefix, source, DSCP, or other criteria.
LSP (Label Switched Path) – ordered sequence of LSRs for one FEC. Unidirectional. Two LSPs needed for bidirectional traffic unless a bidirectional LSP is signalled.
Label stack – multiple labels per packet. BoS=1 indicates the last entry. Enables hierarchy: transport label + service label.
QoS – The three Traffic Class bits define eight distinct priority levels. During congestion, routers apply queue selection based on these bits; this mechanism works irrespective of any IP DSCP value, which is convenient when the IP header is hidden, for example, IPsec-encrypted traffic.
Traffic Engineering (TE) – explicit LSP path control via RSVP-TE. Supports bandwidth reservation, strict/loose hops, and fast reroute.
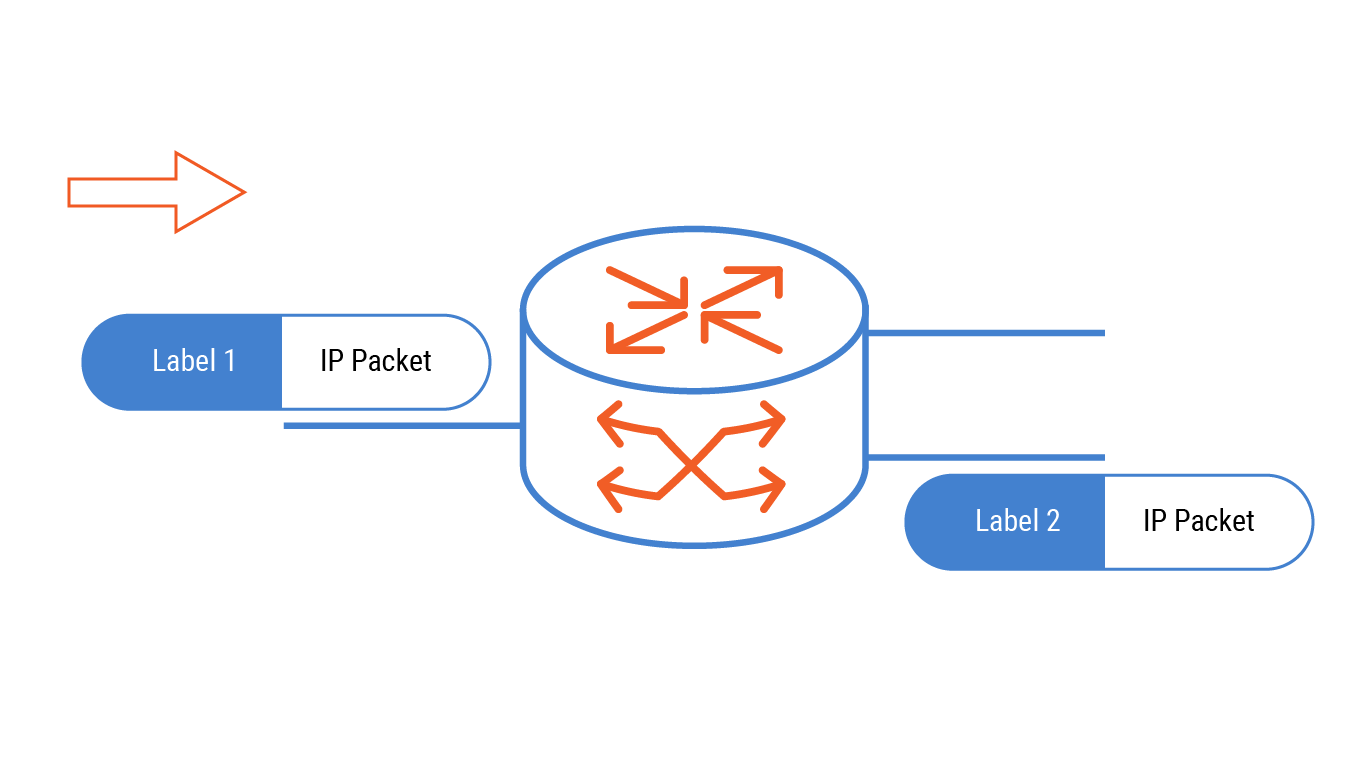
MPLS reduces the time needed to direct packet forwarding by swapping labels instead of performing IP lookups.
LDP vs. RSVP-TE: when to use which
Labels and LSPs do not appear automatically; they are created and distributed by signalling protocols. Two common options are LDP and RSVP-TE. LDP is usually used when MPLS should follow the normal IGP shortest path, while RSVP-TE is used when the operator needs stricter control over the route, bandwidth, or recovery behaviour.
| Feature | LDP | RSVP-TE |
|---|---|---|
| Path selection | Follows IGP shortest path | Explicitly defined, strict/loose hops |
| Bandwidth reservation | No | Yes, admission control |
| Fast Reroute (FRR) | Not native, requires LDP FRR extensions | Built-in, sub-50ms protection |
| Label distribution | Hop-by-hop | Downstream-on-demand |
| Typical use | Best-effort MPLS VPNs | Traffic engineering, latency-sensitive flows |
In practice, many MPLS networks use LDP for standard VPN and transport services because it is simpler to operate. RSVP-TE is more appropriate when traffic engineering is required, especially for latency-sensitive flows, bandwidth-guaranteed services, or fast reroute scenarios.
Why Businesses Use MPLS
MPLS is used when traffic behaviour matters more than simple internet reachability. Common use cases include connecting branch offices to headquarters, carrying voice and video between sites, separating customer traffic in provider networks, supporting regulated industries, and giving critical applications a path backed by measurable SLA targets.
| Business need | MPLS mechanism that addresses it |
|---|---|
| Site-to-site WAN with consistent delay | LSPs remain unchanged across network reconfigurations; forwarding behaviour stays predictable |
| Voice / video | Traffic Class bits prioritise real-time flows over bulk data |
| Private connectivity without encryption | MPLS L3 VPN isolates customer routes natively |
| Contractual performance | SLA with measurable metrics, uptime, latency, jitter, and penalties |
Typical deployments: enterprise WAN, branch-to-HQ; financial trading, latency guarantees; data centre interconnect, stable links for replication; healthcare, SLA-backed uptime.
In practice, an MPLS network is usually invisible to end users. Employees still open applications, make calls, transfer files, and reach remote systems as usual. The difference is in the transport layer underneath: business traffic follows provider-controlled label-switched paths instead of relying only on best-effort internet routing.
MPLS Advantages and Limitations
MPLS is valued because it gives network operators more control over how traffic moves across the WAN. Instead of relying only on best-effort IP forwarding, MPLS can separate traffic, prioritise important applications, and keep packet flows on predictable paths. At the same time, these benefits come with trade-offs: MPLS usually requires provider-managed infrastructure, formal provisioning, and higher recurring costs than internet-based connectivity.
Advantages
The main advantages of MPLS are tied to predictability, traffic control, and service quality. This is why it is often used for business-critical WAN traffic rather than general internet access.
- Deterministic forwarding, exact-match label lookup vs. IP LPM.
- Built-in traffic separation, VPNs without overlays.
- Traffic engineering, path control, bandwidth reservation, FRR.
- Multi-protocol transport, IP, Ethernet, legacy.
Limitations
MPLS is powerful, but it is not the most flexible or cost-efficient option for every traffic type. Its limitations become especially visible when companies need fast cloud access, rapid site deployment, or low-cost bandwidth at many locations.
- Higher cost per Mbps than broadband.
- Slow provisioning, weeks.
- Provider lock-in.
- Inefficient cloud routing, backhaul to hub; direct connect required.
These limitations do not make MPLS outdated, but they explain why many companies now use it selectively. Critical traffic may stay on MPLS, while less sensitive SaaS, web, backup, or guest traffic can move over broadband, DIA, LTE, or other internet-first paths.
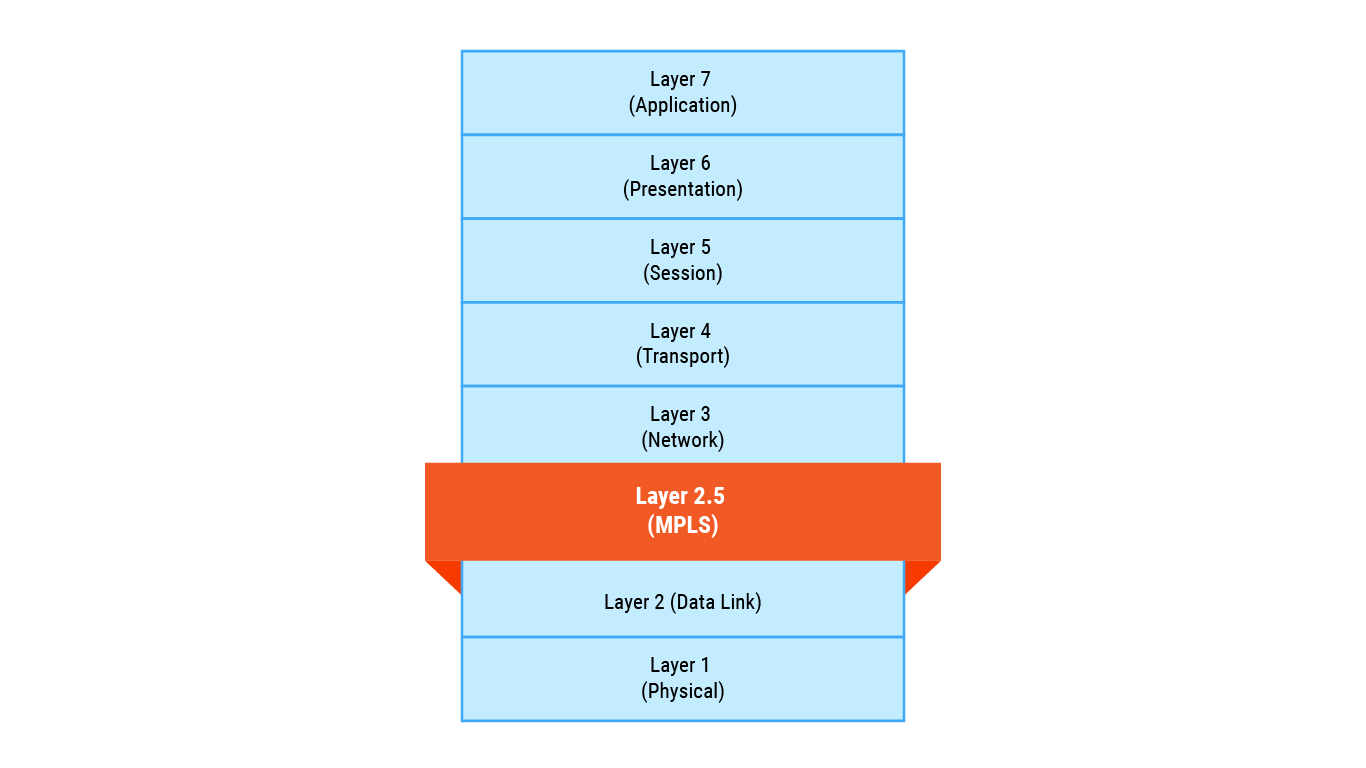
Sitting between Layer 2 & Layer 3, MPLS is considered a Layer 2.5 networking protocol.
Common misconceptions about MPLS
“MPLS is faster than IP routing.” Not necessarily. Modern IP lookups are also done in hardware. MPLS’s advantage is deterministic latency, not raw speed.
“MPLS encrypts traffic.” No. MPLS VPNs isolate routing tables but do not encrypt payloads. For confidentiality, add IPsec or use MACsec on the link.
“MPLS is obsolete because of SD-WAN.” False. SD-WAN often runs over MPLS. MPLS provides the SLA; SD-WAN provides the agility.
Internet-first WANs are cheaper but offer no latency/jitter guarantees. Hybrid WANs use MPLS for critical traffic and broadband for cloud.
Where MPLS Fits in Modern WAN Architecture
In hybrid WAN, an SD-WAN overlay steers traffic:
- Real-time voice/video → MPLS, low latency, QoS.
- Web/email → broadband, low cost.
- Cloud backups → LTE or broadband.
MPLS remains essential for strict SLA applications. It also evolves: Segment Routing MPLS (SR-MPLS) simplifies the control plane; EVPN-MPLS is standard for DCI.
Related Technologies: SD-WAN, EoMPLS, L2VPN/L3VPN
MPLS rarely exists in isolation. In modern enterprise and service-provider networks, it is often used alongside other WAN and VPN technologies: some make traffic management more flexible, others extend Ethernet services between sites, and others help build private networks over an MPLS backbone.
MPLS vs SD-WAN — SD-WAN does not necessarily replace MPLS. In many hybrid WANs, SD-WAN works as an overlay across different connection types, including MPLS, broadband, DIA, and LTE. MPLS remains the transport for critical traffic with latency, jitter, and SLA requirements, while SD-WAN handles path selection and more flexible traffic management.
EoMPLS / Pseudowire — EoMPLS is used when Ethernet traffic needs to be carried across an MPLS network as if there were a direct Layer 2 connection between two sites. This is useful for extending L2 segments, connecting data centres, or scenarios where the customer needs to preserve the Ethernet model over a provider’s MPLS infrastructure.
L2VPN / L3VPN — MPLS is often the foundation for provider VPN services. L2VPN gives the customer data-link-layer connectivity, while L3VPN provides a routed private network with separate routing tables. Both approaches use MPLS to isolate traffic and deliver data between customer sites through the provider’s network.
Key Takeaways
- MPLS is best understood as a managed way to guide business traffic through a network, where packets receive internal forwarding instructions before they cross the provider backbone.
- Its Layer 2.5 role means MPLS does not fully behave like ordinary switching or ordinary IP routing. It works in between: close enough to Layer 2 to use labels, but still able to carry Layer 3 services.
- A packet’s journey through MPLS has three main stages: the provider edge classifies the traffic, the backbone routers move it according to label information, and the far edge returns it to its normal packet format.
- The most important MPLS building blocks are FECs, LSPs, label stacks, QoS markings, and traffic engineering rules. Together, they allow the network to treat selected traffic in a planned and repeatable way.
- Companies usually choose MPLS when ordinary internet transport is not predictable enough for voice, video, branch-to-headquarters traffic, regulated systems, or other applications where delay and service commitments matter.
- MPLS should not be confused with encryption. It can separate routes and support private WAN services, but sensitive data may still need IPsec, MACsec, or another protection method.
- In modern WAN design, MPLS is often used for the traffic that justifies its cost, while broadband, DIA, LTE, SD-WAN, L2VPN, L3VPN, or EoMPLS may cover other connectivity needs.
FAQ
–
+
+
+
+
+
+
+
+
+